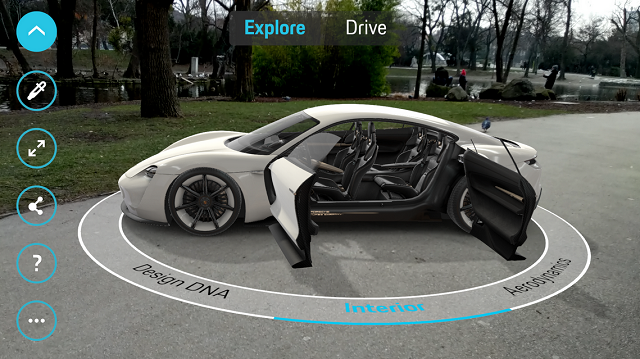
Google’s ARCore to begin its 1.0 journey Google’s ARCore has just entered its 1.0 phase. The...
Sony Introduces Dual-Camera Shooting Solution for Sony RX0
Sony introduces a new trigger cable for the Sony RX0 that allows capture with two cameras Sony has...
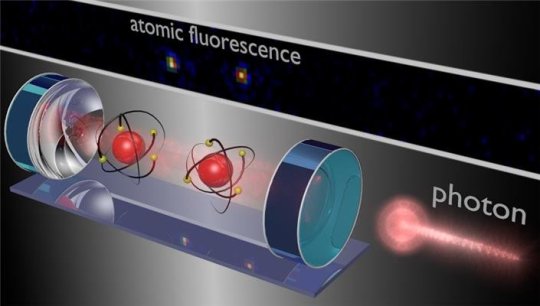
Light Controls Two-Atom Quantum Computation
Scientists Reveal That It the Light Which Controls the Two Atom Quantum Computation We all dream...
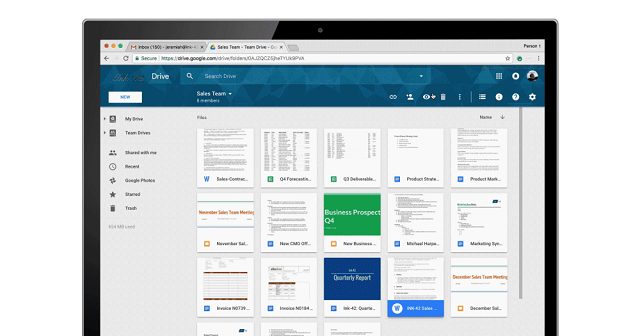
Now Comment On Google Drive Files without Opening Them in Other...
Google Drive Files: We can now make a note on Google Drive files without notching them in other...
Daimler Takes On Silicon Valley with Hi-Tech Mercedes A-Class
Its Daimler VS Silicon Valley on Mercedes A-Class Voice recognition Recently amazon’s Alexa and...
Wearable Technology Could Change the Way Athletes Train
Wearable Technology – The Game Changer in Fitness and Sports Whether it is at the elementary...