Do you want to sell your old MacBook or return a new model that you have bought recently? Then, you...
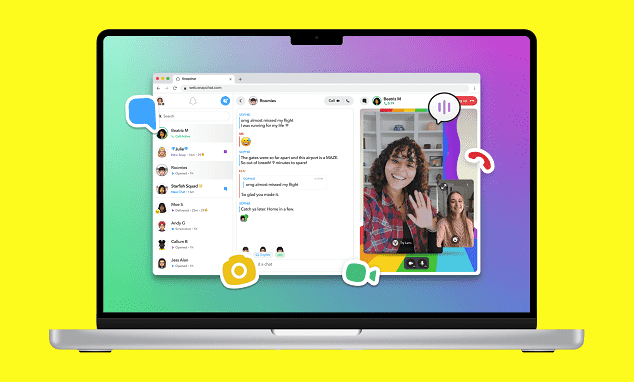
How to Fix Facetime not working on iPhone?
FaceTime is an excellent way through which we can connect with our family & friends. But what...
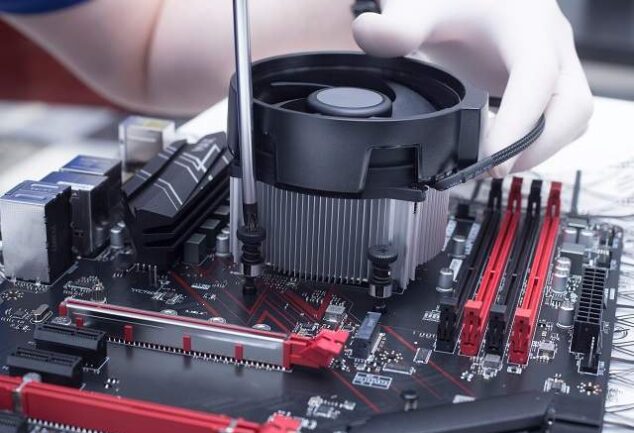
Mac Pro Buyer’s Guide
By launching Mac Pro, Apple has transitioned to Apple silicon across the whole Mac lineup. If you...
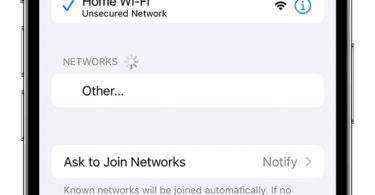
How to Reset Network Settings on iPhone?
If you plan to troubleshoot Wi-Fi, cellular connectivity, or other network-based problems, you must...
Boost Your Website’s Ranking: Best AI SEO Tools for 2024
What are AI SEO Tools? AI SEO tools refer to tools that use artificial intelligence (AI) and...
5 Best Budget Wireless Routers
If you notice, you will get to see that nowadays, the modern workplaces look different than they...
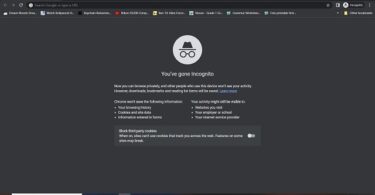
Browse in Private: How to Go Incognito on Chromebook
Privacy is very important for you if you are always working online and using computers. We can run...
Youtube Youre Offline Check Your Connection Error Fixing
Sometimes, when you use YouTube and try to watch a video, you may get the message:...
Sent as SMS via Server What It Mean?
If you are one of the regular mobile users, you can encounter the message “Sent as SMS via...
How to Cheat in Kahoot?
Are you familiar with the technology world? Then, you must know that it is very hard to eliminate...
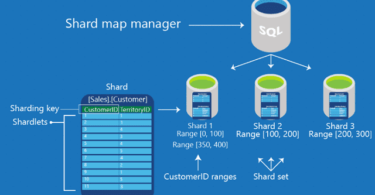
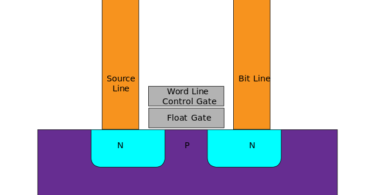
SSD Cache
Usually, the computer system allows the users to store a temporary copy of very frequently used...
10 Best WinRAR Alternatives
Almost every person works with compressed files regularly. Along with consuming less storage space...