Google Play Store is sick with a dubious Android.DoubleHidden Malware
Google Play Store isn’t a highly secure app marketplace but over the Google has boosted his steps to enhance the security on the same. A new Trojan has been unearthed in the Google Play Store which makes use of some sophisticated techniques to hide it securely on the devices. This malicious app is Android.DoubleHidden Malware which exclusively collects device information and displays advertisements. The worst thing about this Android.DoubleHidden is that its capability can be enlarged by the hackers to use it for other malicious purposes.
The fascinating alternating personality Android.DoubleHidden
This Android.DoubleHidden malware comes within malicious app called ‘Photograph by Fiery’ as translated in English from its Persian origin. It package name is com.aseee.apptec.treeapp. The way this app is being made available to the customers is such that it the author doesn’t come under the Google’s radar. Within last two months of October and November this app has already been updated more than five times.
The author smartly ensures that this malicious Android.DoubleHidden app keeps alternating between working as the normal legitimate photo editing app and a self-hiding malicious non-app. The way it alternates between its two personalities is quite fascinating for the security researchers. The developer or author of this app goes by the name ‘i.r.r developers’ who is known to publish a larger of number of apps which are completely legitimate.
Android.DoubleHidden dupes you in every manner
This Android.DoubleHidden app showcases itself just like any other photo editing app but soon it hides itself just after the installation leaving the users distraught. Upon launch Android.Doublehidden specifically asks users to provide Device Administrator permissions which help it in gaining a strong control over the device. After taking permissions for all the controls the screen will light with a messages stating that this app can’t work on the given phone device. The notoriously aspect of this message is that it in the second line it states that after exiting this application will be deleted.
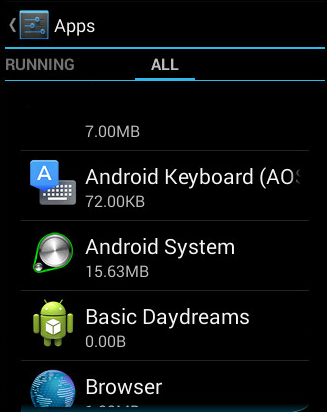
The dangerous part of this app is that not just it closes but it remains hidden with all its malicious functionality intact though users feel that the app has been uninstalled from the device. It remains hidden on the mobile device by placing a transparent image without any app name. If you go into the ‘Settings’ to search for the app then you will find a blank entry wherever it is displayed. Android.Doublehidden makes use of set
ComponentEnableSetting()code which allows app to disappear after it launched from the app launcher. In other words no icon can be seen on the homes screen or in the Settings of the mobile. This
Android.DoubleHidden malware specifically collects user’s data and works on the basis of advertising revenue. It also actively collects user information and actively sends to the malware authors. The information collected by this malware includes IMEI number, device model, Mac address, device brand, device screen, network connectivity, location along with the applications running right in the foreground as well as other all accounts listed with the Account Service.







