Network Layer Protocol – Data & Communication Transmission
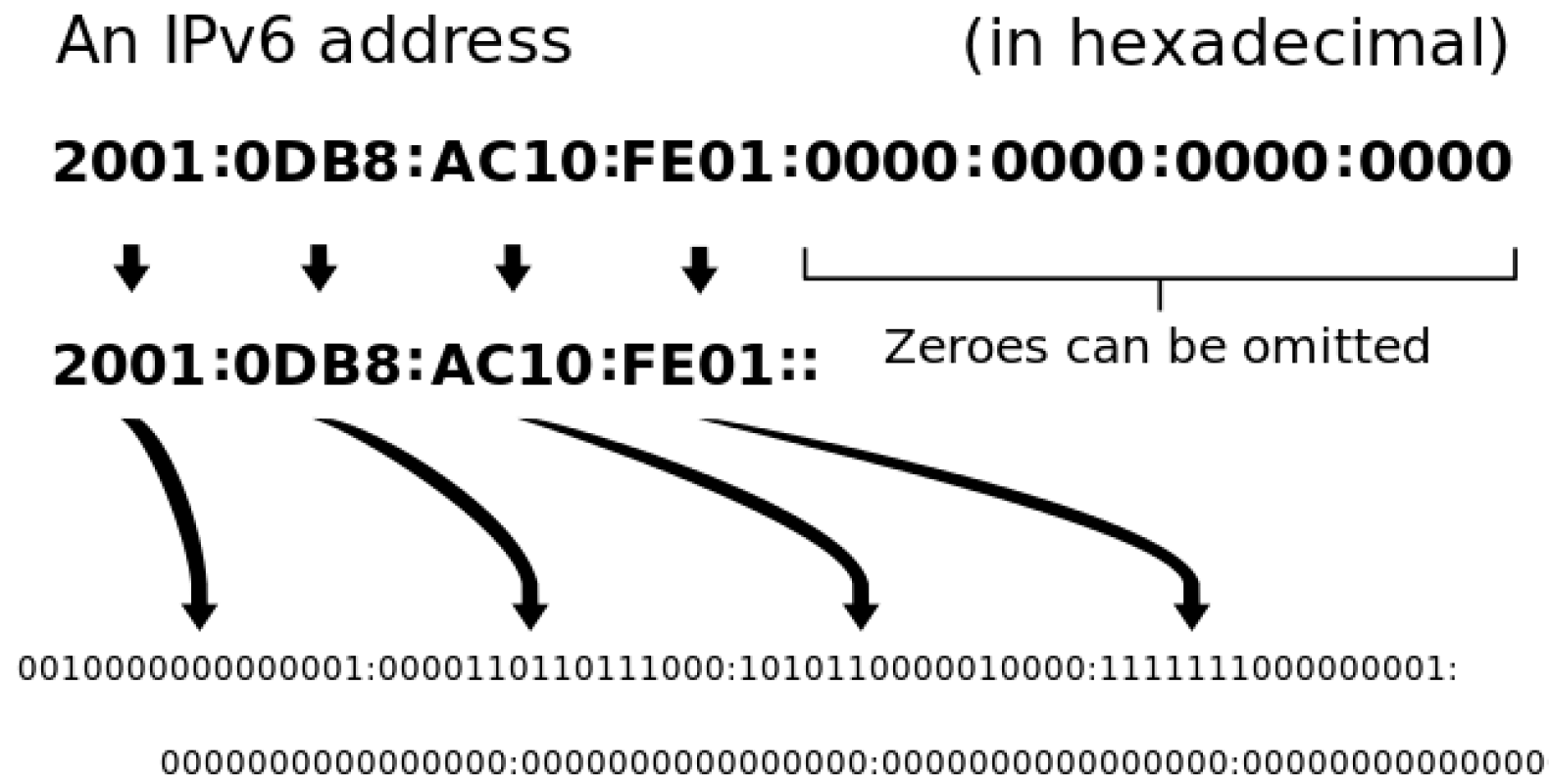
The latest type of Internet Protocol (IP) is the Internet Protocol version 6 (IPv6)which is the communication protocol offering aproof of identity together with location system for the computers on networks as well as routes the traffic across the Internet. It is a network layer protocol enabling data and communication transmission to occur over the network and came into existence in 1998 to take over and replace IPv4 protocol someday. Established by the Internet Engineering Task Force (IETF), in 1998, IPv6 tends to deal with the long-expected issue of IPv4 address exhaustion. The IPv4 protocol comprises of four number strings each of which has three digits divided by dots. A standard IPv4 address has 32-bit which seems like 255.255.255.255 enabling 4.2 billion unique IP addresses. With the increase in wireless and network friendly devices on the rise, it is speculated that very soon the internet may get exhausted of all unique IPv4 addresses. In order to resolve this issue a new standard of network layer protocol enabling more unique IP address was created and IPv6 was standardized. IPv6 protocol comprising of 128-bits has eight numbered strings where the individual has four characters –alphanumeric disconnected by colon which provides an incredibleamount of unique IP addresses.
IPv4 Infrastructure – Carry IPv6 Packets – Tunnelling
More addresses would be essential in connecting devices than those available on the IPv4 address space and it also assures that we will not run out of unique IP address to assign to new devices shortly. The actual number tends to be somewhat smaller, as multiple ranges have been set aside for special use or totally excluded from usage. The two protocols have not been developed to be interoperable, complicating the transition to IPv6 but most of the IPv6 transition mechanisms are formulated to enable communication between IPv4 and IPv6 hosts. Several Internet users do not tend to have IPv6 dual-stack support. Hence they are unable to directly reach sites. They need to utilise IPv4 infrastructure in order to carry packets which is done by using a method called tunnelling that captures IPv6 packets in IPv4, basically utilising IPv4 as a connection layer for IPv6. There are various types of addresses-
- Unicast addresses – which identifies unique node on a network and is inclined in referring to an individual sender or receiver
- Multicast addresses which represents a group of IP devices which can be utilised only as the destination of a datagram
- Anycast addresses is assigned to a set of interfaces which tend to belong naturally to various nodes
The Advantages of it
- Routing competence
- Stringer safety
- Consistency
- Quicker speeds
- Worldwide reachability
- Superior encryption
- Higher website adaptation
- Enhanced user experience
- Improved customer insights
The Disadvantages of IPv6
Conversion – IPv4 tends to be yet very popular and many including users and companies have been taking their time in making the modification to v6.
Communication– IPv4 and IPv6 mechanisms does not have the capacity of communicating directly with each other and to make it possible would need intermediate equipment.
Transition – A lot of effort together with numerous hours of work would be needed for the user to switch from IPv4.
Readability–In comparison to IPv4, v6 sub-netting tends to be complex to understand while recalling your v6 address is almost impossible.
Who should care about IPv6 Address and Why
Network Layer protocol is appropriate choice for professional users together with home-based users and is perfect for Network engineers, data centres, mobile carriers, and tech companies.
When is the Identity leaked by IPv6
Though there is no harm linked with IPv6 addresses but it could be a bit complicated when users tend to link to a VPN. A VPN user is assigned an IPv4 IP address when they are connected to a VPN wherein the user makes attempts in communicating with an IPv6 server. However there could be instances where the real IP address could get leaked and could lead to exposed identity.
How could one get protection from IPv6 Leak with Pure VPN
The leakage could be a threat wherein it could disclose one’s identity without the user being aware of it. It is always beneficial to put in extra efforts in safeguarding one’s personal information from being tracked or recorded by any unauthorized individual or team. This can be done with ease by disabling its ability from the machine each time a user would need to link to a VPN. When the private session has been accomplished, then the ability can be enabled which can be done with a single click. One of the best tools in the market which tends to be helpful to protect your IPv6 address from leaking your real information and your personal details is PureVPN. User could take the opportunity of subscribing to any of the premium plans of PureVPN in order to avail total IPv6 security.